How to Segregate IoT, Security, Guest, and Private Networks While Allowing Communication with Home Assistant
 A Beginner’s Guide to VLAN Segmentation for Smart Homes
A Beginner’s Guide to VLAN Segmentation for Smart Homes
 Understanding VLAN Segmentation
Understanding VLAN Segmentation
A VLAN (Virtual LAN) allows you to separate your devices into isolated networks while still allowing controlled communication where needed. This enhances security, performance, and organization.
 Recommended VLAN Setup
Recommended VLAN Setup
Since you have a Sophos XG router, VLAN-capable switch, and Unifi APs, you should create separate VLANs for different device categories:
| VLAN |
Purpose |
Example Devices |
Recommended Subnet |
| Private (Trusted LAN) |
Main devices that need full access & security |
PCs, laptops, Home Assistant VM, NAS |
10.10.40.0/24 |
| IoT (Untrusted LAN) |
Smart home devices with limited internet & inter-device access |
Smart plugs, bulbs, thermostats |
10.10.10.0/24 |
| Security (Cameras & NVRs) |
Isolated for security with access only to storage |
Cameras, NVR, doorbell cam |
10.10.30.0/24 |
| Guest (Isolated Internet-Only) |
For visitors, no access to other devices |
Phones, tablets |
10.10.60.0/24 |
 Your Home Assistant (HA) should stay on the Private VLAN (
Your Home Assistant (HA) should stay on the Private VLAN (10.10.40.x) since it acts as the main controller.
 Wi-Fi & VLANs on Unifi
Wi-Fi & VLANs on Unifi
Since you have Unifi APs, you can create multiple SSIDs and tag them with the appropriate VLANs:
 “Home Wi-Fi” → VLAN 40 → Trusted, full access
“Home Wi-Fi” → VLAN 40 → Trusted, full access
 “IoT Wi-Fi” → VLAN 10 → Restricted, only communicates with HA
“IoT Wi-Fi” → VLAN 10 → Restricted, only communicates with HA
 “Guest Wi-Fi” → VLAN 60 → Internet-only, no LAN access
“Guest Wi-Fi” → VLAN 60 → Internet-only, no LAN access
 Getting IoT Devices to Communicate with Home Assistant
Getting IoT Devices to Communicate with Home Assistant
Q: “Do I need to put HA on IoT VLAN?”
No! You want HA on the Private VLAN (10.10.40.x), but you need to allow select traffic from IoT VLAN (10.10.10.x) to HA.
 Step 1: Configure VLANs on Your Sophos XG Router
Step 1: Configure VLANs on Your Sophos XG Router
You will create VLAN interfaces under your LAN interface and assign each VLAN an IP range.
Example:
VLAN 10 (IoT) → 10.10.10.1/24VLAN 30 (Security) → 10.10.30.1/24VLAN 40 (Private) → **10.10.40.1/24`VLAN 60 (Guest) → 10.10.60.1/24
 Step 2: Firewall Rules to Allow IoT to Talk to HA
Step 2: Firewall Rules to Allow IoT to Talk to HA
By default, VLANs should not communicate. You must create firewall rules to allow IoT devices to talk to Home Assistant.
 Allow IoT VLAN to Access HA (but nothing else)
Allow IoT VLAN to Access HA (but nothing else)
In Sophos XG Firewall Rules, create:
| Source |
Destination |
Ports |
Action |
Purpose |
10.10.10.0/24 (IoT) |
10.10.40.21 (HA) |
8123 (HA UI), 5353 (mDNS), 1883 (MQTT) |
Allow |
Let IoT devices talk to HA |
10.10.10.0/24 (IoT) |
ANY |
* |
Deny |
Block IoT from accessing Private LAN |
 This allows IoT devices to talk to HA but prevents them from accessing PCs, NAS, or other private devices.
This allows IoT devices to talk to HA but prevents them from accessing PCs, NAS, or other private devices.
 Step 3: Allow IoT Discovery with mDNS
Step 3: Allow IoT Discovery with mDNS
Many IoT devices discover HA using mDNS (Multicast DNS). However, mDNS is local to a VLAN and won’t work across VLANs by default.
 Solution: Enable mDNS Reflector in Sophos XG
Solution: Enable mDNS Reflector in Sophos XG
- In Sophos XG, enable
avahi-daemon or mDNS Repeater.
- This lets IoT devices discover HA even when they are on different VLANs.
 Step 4: Assign VLANs to Switch Ports
Step 4: Assign VLANs to Switch Ports
Since you have a VLAN-capable switch, configure the ports correctly:
- Trunk Ports (carry multiple VLANs) → Connects to Router & Unifi APs
- Access Ports (single VLAN) → IoT devices, Security devices, NAS, etc.
 Example VLAN Port Setup:
Example VLAN Port Setup:
| Device |
VLAN Mode |
VLAN ID |
| Router to Switch |
Trunk |
All VLANs |
| Unifi APs |
Trunk |
10,40,60 |
| Home Assistant VM |
Access |
40 |
| IoT Wired Device |
Access |
10 |
| NAS |
Access |
40 |
 Step 5: Assign VLANs in Synology NAS & Home Assistant
Step 5: Assign VLANs in Synology NAS & Home Assistant
- Synology NAS → Put it in Private VLAN (
10.10.40.x)
- Home Assistant VM → Assign Private VLAN (
10.10.40.x)
 If your HA is running in a VM on the NAS, you may need to enable VLAN tagging in the VM settings.
If your HA is running in a VM on the NAS, you may need to enable VLAN tagging in the VM settings.
 Final Recap:
Final Recap:
 Use VLANs to separate IoT, Private, Security, and Guest devices.
Use VLANs to separate IoT, Private, Security, and Guest devices. Put HA in Private VLAN (
Put HA in Private VLAN (10.10.40.x) and allow IoT VLAN (10.10.10.x) to talk only to HA. Set up VLANs in Unifi for Wi-Fi SSIDs (Home, IoT, Guest).
Set up VLANs in Unifi for Wi-Fi SSIDs (Home, IoT, Guest). Enable mDNS Reflector in Sophos XG to allow IoT discovery.
Enable mDNS Reflector in Sophos XG to allow IoT discovery. Properly configure firewall rules to isolate IoT but allow necessary communication to HA.
Properly configure firewall rules to isolate IoT but allow necessary communication to HA.
 Basic Firewall Rules for VLAN Segmentation in Sophos XG
Basic Firewall Rules for VLAN Segmentation in Sophos XG 
(A Beginner’s Guide to Securing IoT & Home Assistant Networks)
Since you’re using Sophos XG, you’ll need firewall rules to properly segregate VLANs while allowing necessary communication (e.g., IoT → Home Assistant).
 Step 1: Access Sophos XG Firewall Rules
Step 1: Access Sophos XG Firewall Rules
 Log into Sophos XG Admin UI
Log into Sophos XG Admin UI
 Go to → Rules & Policies > Firewall Rules
Go to → Rules & Policies > Firewall Rules
 Click “Add Firewall Rule”
Click “Add Firewall Rule”
 Step 2: Create Essential Rules
Step 2: Create Essential Rules
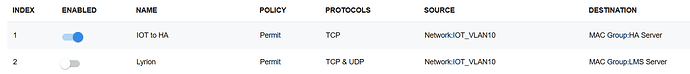
 Rule 1: Allow IoT Devices to Talk to Home Assistant
Rule 1: Allow IoT Devices to Talk to Home Assistant
- Source Zone: IoT VLAN (
10.10.10.0/24)
- Destination Zone: Private VLAN (
10.10.40.21 - Home Assistant)
- Services (Ports):
8123 (Home Assistant Web UI)5353 (mDNS for device discovery)1883 (MQTT if you use it)
- Action: Allow
- Log Traffic?
 (Good for debugging!)
(Good for debugging!)
 This rule allows IoT devices to control smart home services without accessing other private devices.
This rule allows IoT devices to control smart home services without accessing other private devices.
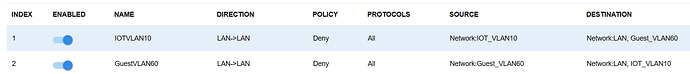
 Rule 2: Block IoT Devices from Everything Else
Rule 2: Block IoT Devices from Everything Else
- Source Zone: IoT VLAN (
10.10.10.0/24)
- Destination Zone: Private VLAN, Security VLAN, Guest VLAN
- Services: All
- Action: Drop/Block
- Log Traffic?
 (Helps catch misbehaving devices!)
(Helps catch misbehaving devices!)
 This prevents IoT devices from reaching personal computers, NAS, etc.
This prevents IoT devices from reaching personal computers, NAS, etc.
 Rule 3: Allow Home Assistant to Talk to IoT Devices
Rule 3: Allow Home Assistant to Talk to IoT Devices
- Source Zone: Private VLAN (
10.10.40.21 - HA)
- Destination Zone: IoT VLAN (
10.10.10.0/24)
- Services:
5353 (mDNS)443 / 80 (API Calls)1883 (MQTT if used)
- Action: Allow
 This lets HA control smart devices like lights, switches, thermostats.
This lets HA control smart devices like lights, switches, thermostats.
 Rule 4: Allow Private Devices (PCs, Phones) to Access HA
Rule 4: Allow Private Devices (PCs, Phones) to Access HA
- Source Zone: Private VLAN (
10.10.40.0/24)
- Destination Zone: Private VLAN (
10.10.40.21 - HA)
- Services:
8123 (HA UI)
- Action: Allow
 This allows you to access HA UI from your PC or phone.
This allows you to access HA UI from your PC or phone.
 Rule 5: Block Guest VLAN from Accessing Anything
Rule 5: Block Guest VLAN from Accessing Anything
- Source Zone: Guest VLAN (
10.10.60.0/24)
- Destination Zone: Any Internal VLAN
- Action: Drop/Block
- Log Traffic?

 Guests should only get internet access, not access to IoT, security cameras, or HA.
Guests should only get internet access, not access to IoT, security cameras, or HA.
 Rule 6: Allow Security Cameras to NAS (NVR Storage)
Rule 6: Allow Security Cameras to NAS (NVR Storage)
- Source Zone: Security VLAN (
10.10.30.0/24)
- Destination Zone: NAS VLAN (
10.10.40.30 - Synology NAS)
- Services:
NFS, SMB, RTSP
- Action: Allow
 This lets cameras save footage to your NAS/NVR but blocks them from accessing the internet or private network.
This lets cameras save footage to your NAS/NVR but blocks them from accessing the internet or private network.
 Final Rule Order in Sophos XG
Final Rule Order in Sophos XG
Sophos processes firewall rules in order, so position matters! Arrange rules like this:
| # |
Rule Name |
Source |
Destination |
Ports |
Action |
 |
IoT → HA (Allow) |
10.10.10.0/24 |
10.10.40.21 |
8123, 5353, 1883 |
 Allow Allow |
 |
IoT → Private, Security, Guest (Block) |
10.10.10.0/24 |
10.10.40.0/24, 10.10.30.0/24, 10.10.60.0/24 |
All |
 Block Block |
 |
HA → IoT (Allow) |
10.10.40.21 |
10.10.10.0/24 |
5353, 443, 1883 |
 Allow Allow |
 |
Private → HA (Allow) |
10.10.40.0/24 |
10.10.40.21 |
8123 |
 Allow Allow |
 |
Guest → Private, IoT, Security **( |
|
|
|
|
This is basic and where I started with my firewall and rules as well when migrating. It’s a learning journey and if it captures your interest, a major time yanker  Good luck!
Good luck!