I finally took the time to setup wildcard certifications and wanted to share the setup process with the awesome HA-Community 
Background
I’m using Reverse proxy on Synology and my wife was having problems accesing the Blue Iris webpage and other services that was behind the reverse proxy. Mainly because of the browser complaining about the cert not beeing trusted and you have to manually overide that. To much of a struggle.
Solution is to issue wildcard certs but unfortunatly Synology only support that for it own DDNS from web GUI. So instead we will be issuing certs using acme.sh and then deploy the certs to Synology. aceme.sh should also let us to be able to not have to expose port 80 for cert renewal but I haven’t tested this. Please, share your findings in the coments.
For this guide I’m basically using the official guide on:
Installation of acme.sh
$ sudo su
$ cd ~
$ wget https://github.com/acmesh-official/acme.sh/archive/master.tar.gz
$ tar xvf master.tar.gz
$ cd acme.sh-master/
$ ./acme.sh --install --nocron --home /usr/local/share/acme.sh --accountemail "email@gmailcom"
$ source ~/.profile
Creating the certificate
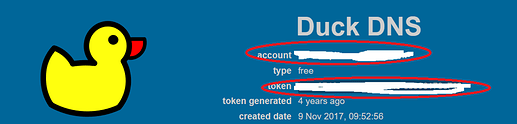
Get your token by logging into DuckDNS
$ cd /usr/local/share/acme.sh
export DuckDNS_Token="aaaaaaaa-bbbb-cccc-dddd-eeeeeeeeeeee"
Please note that since DuckDNS uses StartSSL as their cert provider, thus --insecure may need to be used when issuing certs:
./acme.sh --insecure --issue --dns dns_duckdns -d *.mydomain.duckdns.org
I got problems issuing the standard cert, the cert without wildcard wich is needed if you want to use mydomain.duckdns.org link. adding --domain-alias mydomain.duckdns.org’ like this fixed it:
./acme.sh --insecure --issue --dns dns_duckdns -d *.mydomain.duckdns.org --domain-alias mydomain.duckdns.
I had a little bit of problem with this step and got error:
No EAB credentials found for ZeroSSL.
After changing default ca server to letsencrypt it worked fine:
/root/.acme.sh/acme.sh --set-default-ca --server letsencrypt
Deploy the default certificate
We will use the Synology DSM deployhook to deploy our certificate. This will override the default certificate, in the next section you can see how to create new certificates to be used for other services.
$ cd /usr/local/share/acme.sh
# Single quotes prevents some escaping issues if your password or username contains certain special characters
$ export SYNO_Username='Admin_Username'
$ export SYNO_Password='Admin_Password!123'
$ export SYNO_Create=1
# You must specify SYNO_Certificate, for the default certificate, we use an empty string
# Please be aware that the empty string only works if you haven't added/changed the description for
# the default certificate. If you have, you'll need to specify the description here.
# SYNO_Create=1 This tells acme.sh to create a new certificate in the DSM if it isn't already
$ export SYNO_Certificate=""
$ ./acme.sh --deploy --home . -d *.mydomain.duckdns.org --deploy-hook synology_dsm
[Update 2023-10-02]
I had to change the deploy command to:
./acme.sh --deploy -d *.mydomain.duckdns.org --deploy-hook synology_dsm --debug
I also had problems deploying multiple certs (both the wildcard and the cert without wildcard) I tried so just create the cert without wildcard in synology but had by this point created to many lets encrypt certs.
I ended up copying my cert to a place were it’s accessible from filestation in synology
like this:
ash-4.4# cp /root/.acme.sh/domain.duckdns.org/domain.duckdns.org.cer /volume1/music/domain.duckdns.org.cer
ash-4.4# cp /root/.acme.sh/domain.duckdns.org/domain.duckdns.org.key /volume1/music/domain.duckdns.org.key
ash-4.4# cp /root/.acme.sh/domain.duckdns.org/ca.cer /volume1/music/ca.cer
ash-4.4# cp /root/.acme.sh/domain.duckdns.org/fullchain.cer /volume1/music/fullcahain.cer
After this I could manually import it in Synology like this:
Check the certificate in Synology DSM
Now we should be able to see our new wildcard cert in SynologyDSM
Don’t forget to assign wich cert to use with wich domain under properties
Configuring Certificate Renewal
To auto renew the certificates in the future, you need to configure a task in the task scheduler. It is not advised to set this up as a custom cronjob (as was previously described in this wiki page) as the DSM security advisor will tell you that you have a critical warning regarding unknown cronjob(s).
In DSM control panel, open the ‘Task Scheduler’ and create a new scheduled task for a user-defined script.
- General Setting: Task - Update default Cert. User - root
- Schedule: Setup a weekly renewal. For example, 11:00 am every saturday.
- Task setting: User-defined-script:
renew certificates
/usr/local/share/acme.sh/acme.sh --cron --home /usr/local/share/acme.sh/
Thats it!
You should now be able to enjoy wildcard certs with DuckDNS!